
Wireless Energy Monitoring: Addressing the Security Questions IT Leaders Ask
Every energy monitoring project that involves wireless sensors and cloud connectivity eventually arrives at the same conversation with the IT security team. The questions are predictable, legitimate, and important: How does data leave the building? What network infrastructure does this touch? Who can access the data? How is it secured in transit and at rest? Can this system be used as an attack vector into our operational technology environment? These are exactly the right questions, and the good news is that the answers for modern wireless energy monitoring architectures are reassuring.
Understanding the security architecture of a wireless energy monitoring system requires separating it into its constituent components: the sensors themselves, the bridge device that communicates with sensors and transmits data to the cloud, the network connectivity, and the cloud platform.
The Sensor Layer: Secure by Design
Wireless energy sensors in a properly designed monitoring system communicate exclusively with their paired bridge device using a proprietary wireless protocol. They do not use Wi-Fi, Bluetooth, Zigbee, or any other consumer wireless protocol. They do not connect to the internet. They do not connect to the building's IT network. They communicate only with the bridge that was configured at installation time.
This is an important security property. A sensor that communicates only on a proprietary protocol with a specific, paired gateway cannot be used as an entry point into the building's network infrastructure. It has no IP address, no network stack, and no attack surface from a network security perspective. The sensor layer is effectively air-gapped from the building's IT and OT networks.
The sensors are also read-only devices. They measure electrical current and transmit that measurement data. They receive no commands, have no control capability, and cannot interact with the circuits they monitor in any way other than measuring them. There is no possible attack scenario in which a compromised energy sensor could affect building operations, because the sensors have no actuator capability of any kind.
The Bridge Layer: The Connectivity Point
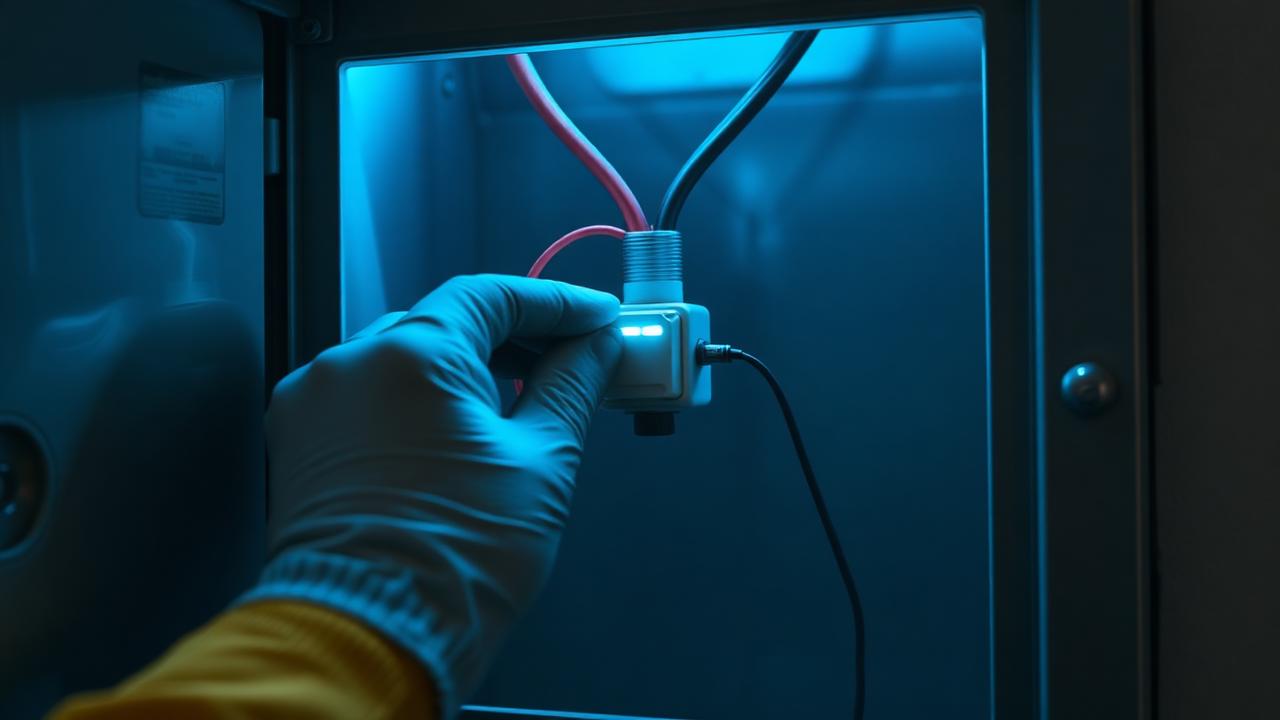
The bridge device — the hardware that collects data from sensors and transmits it to the cloud — is the point in the architecture that connects the sensor network to the broader IT infrastructure. Understanding its security properties is therefore the most important part of the security analysis.
Modern monitoring bridges connect to the cloud over standard HTTPS — the same encrypted protocol used for online banking and e-commerce. All data transmitted from the bridge to the cloud is encrypted in transit using TLS encryption. The bridge communicates on port 443, the standard HTTPS port, which is already permitted outbound on virtually all corporate firewalls. No special firewall rule changes are required for cloud connectivity.
The bridge does not accept inbound connections from the internet. It initiates outbound connections to the cloud platform to transmit data, but no external party can initiate a connection to the bridge. This outbound-only communication model is the same architecture used by many corporate IoT and OT monitoring devices and is well understood by IT security teams.
From a network segmentation perspective, the bridge is typically placed on the building's operations network — the same VLAN used for BMS controllers, access control panels, and other building systems — or on a dedicated IoT network segment. It is not placed on the corporate IT network used for user workstations and servers. This segmentation ensures that even in the unlikely event of a bridge compromise, the exposure is limited to the building systems network segment, not the broader corporate environment.
The Cloud Platform: Data Access Controls
Energy monitoring data collected by the sensor and bridge infrastructure is transmitted to and stored in a cloud platform. The security properties of this platform — data encryption at rest, access control mechanisms, authentication requirements, and data retention policies — are legitimate subjects of IT security due diligence.
Well-designed commercial energy monitoring platforms use industry-standard security practices: AES-256 encryption for data at rest, TLS 1.2 or higher for data in transit, role-based access control with multi-factor authentication for user accounts, and SOC 2 Type II certification confirming that security controls have been independently audited.
Data stored in the platform is limited to energy consumption measurements — timestamps and current readings from each sensor. It contains no personally identifiable information, no financial data, and no information that would be of value to an adversary outside the building energy management context. The data classification is operational technology telemetry — a category that generally receives the same or lower data protection requirements than corporate business data.
The Modbus TCP Integration: The OT Security Question
In deployments where circuit monitoring data is integrated into a building management system using Modbus TCP, the IT security question becomes more complex — because Modbus TCP is a legacy protocol without native authentication or encryption, operating on the OT network.
This concern is legitimate but manageable with standard OT security practices. Modbus TCP communication between the monitoring bridge and the BMS server occurs on the internal building automation network, not over the internet. Network-level controls — firewall rules that restrict Modbus TCP communication to specific source and destination IP addresses, network monitoring for anomalous Modbus traffic — are standard practices in secured OT environments and are compatible with the integration architecture.
Organizations with mature OT security programs — particularly in healthcare, critical infrastructure, and financial services — may also choose to implement a data diode or one-way gateway that permits data flow from the monitoring bridge to the BMS server while preventing any return communication, eliminating the Modbus attack surface entirely.
The security architecture of modern wireless energy monitoring systems has been designed with these IT security concerns in mind. The conversations with IT security teams are important and appropriate, and they can be navigated successfully with the right documentation and a clear explanation of how the architecture addresses each concern.
Ready to get started? Emergent Energy installs and integrates Panoramic Power wireless energy monitoring systems — circuit-level intelligence deployed in hours, not weeks. Contact us for a facility assessment and ROI estimate.
Ready to reduce your facility's energy costs?
Explore Emergent Energy's monitoring, rebate, and procurement services.
Related Articles
Non-Invasive Installation: Why Zero-Downtime Monitoring Is a Game Changer for 24/7 Operations
Self-powered, clamp-on wireless sensors deploy across hospitals, plants, data centers and hotels in days — without a single panel shutdown or operational interruption.
Read more
BMS Integration: Making Your Building Management System Smarter with Circuit-Level Data
How Modbus TCP integration between wireless circuit monitoring and existing BMS platforms transforms control systems into true energy intelligence platforms — accelerating retrocommissioning and enabling automated demand management.
Read more
Three Sustainability Deadlines That Define the Next 100 Days for U.S. Operators
A Friday roundup of the energy data, REC market, and packaging compliance deadlines shaping how PA and U.S. operators plan the rest of 2026.
Read more